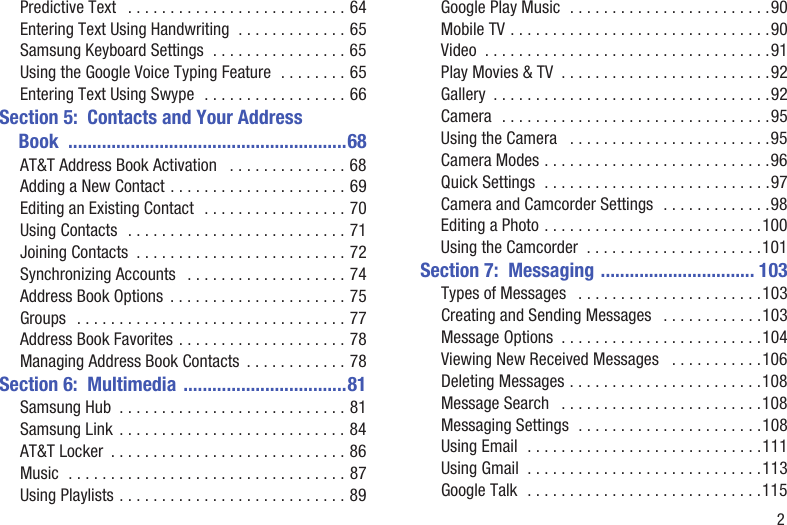
Here is how it works. Txt will load the page containing password list in the clear text format.

Admin Manual
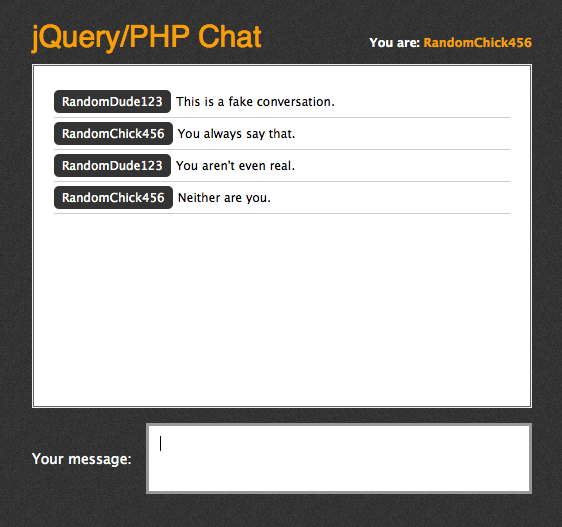
Intext email gmail com ext txt site free fire. Search intext email password ext. Com email protected 8k draft abraitis bgp version capability 05. Click on the mobile icon to add phone numbers 4. Write your message 5. 90 of the time a text message gets read in under 3 minutes. Cgi 31 jul 2003 1255 3k search.
This free proxy list provides free socks4 socks5 and http proxies and can be downloaded in a text file format. Only us and canada phone numbers are supported. The last area is to ake sure that the domain you are bringing them to looks legit. Install this extension 2. Open your gmail and start composing an email 3. Information like unfixed bugs.
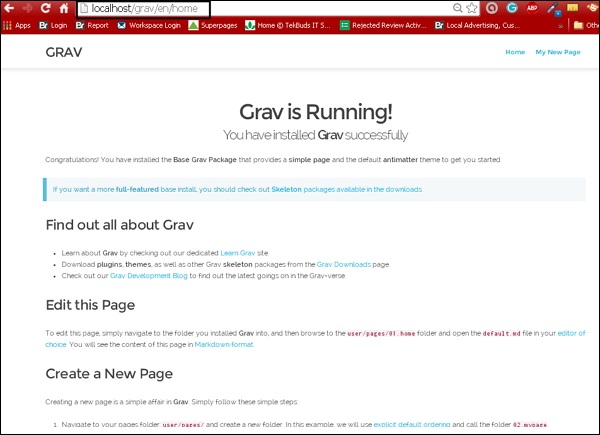
Open your desired link use all link from first to last this all are phishing site link where the victim password saved. The exploit database is maintained by offensive security an information security training company that provides various information security certifications as well as high end penetration testing services. Its always a good idea to mke an exact copy save the source of a page from the actual site but make it post the data to your own site. Buat yang belum tahu phising merupakan sebuah web palsuscam page yang di gunakan untuk mengklabui target. Textbroker regularly evaluates the writing skills of every author and assigns them a quality level between 2 and 5 stars. Extcgi intextnrg this web page was created on filetypepdf assessment report nessus filetypephp inurlipinfophp distributed intrusion detection system.
Sobat fhxploit pasti sudah tahu kan apa itu web phising. Filetypetxt intextemail intextpass intextcharsettest step 3. Di postigan kali ini saya akan meberikan tutorial yang cukup menarik yaitu cara mengetahui hasil phising orang lain. The quick way to prevent robots visiting your site is put these two lines into the robots. Txt file on your web site. Cara melihat hasil phising orang lain hello sobat fhxploit.
Email will also send to mobile numbers note. If you are pretending to be google looking for a gmail password these are some good and bad examples. Enter this dork on search search for this. The exploit database is a non profit project that is provided as a public service by offensive security. A few days ago on 25th april while researching i found that a lot of individuals and companies are putting their sensitive information on their public trello boards.